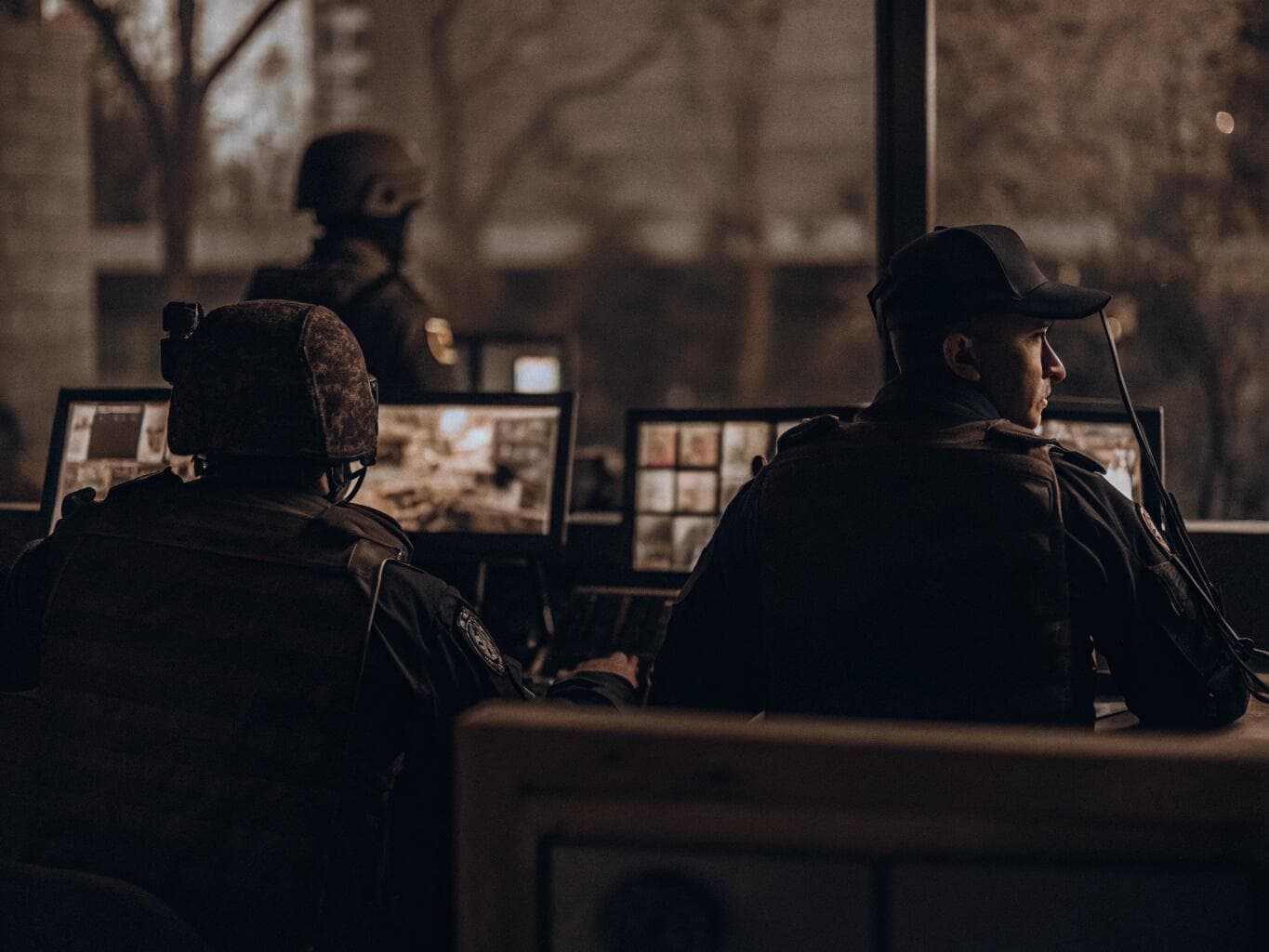
Detect Threats Before They Become Incidents
Overview
Most organizations discover threats after damage occurs. By the time patterns are noticed (social media clusters, sensor sequences, unusual event combinations near sensitive locations), the prevention window has closed. TACCS™ uses patented AI to continuously monitor data streams for conditions and patterns requiring immediate attention.
How It Works
TACCS™ monitors alerts from data streams to identify threat patterns and provides automated notification or initiates action. Detects simple to complex patterns.
Specific Event Detection
The occurrence of a specific event type in a defined area that could cause loss or impairment of identified assets or resources — for example, social media reports of illness combined with reduced supplies of medication in a region.
Complex Pattern Recognition
Sequences of occurrences within defined times and locations that constitute an indicator of possible hostility — such as the digital signatures of an emerging cyber-attack.
Trend Analysis
Conditions that are impairing or may impair a mission over time — for example, rising crime rates near multiple sensitive locations.
Predictive Analytics
Projected impact of identified threats on key resources and critical infrastructure, giving leadership the information they need to plan a response before the threat materializes.
Technical Foundation
Patent Nos. 9,024,757 and 9,727,822. Open architecture and extensive APIs accommodate agentic AI feeds. Demonstrated during COVID-19 integrating IBM pandemic data for National Guard in JAIC project.
Who It’s For
Security operations managers, intelligence analysts, operations center directors, protective detail leaders, senior executives.
Don’t wait for the post-incident report to find the warning signs.
See how TACCS™ patented AI identifies threats while there’s still time to act.
Schedule a Demo →